Civil Liberties and Law in the Era of Surveillance
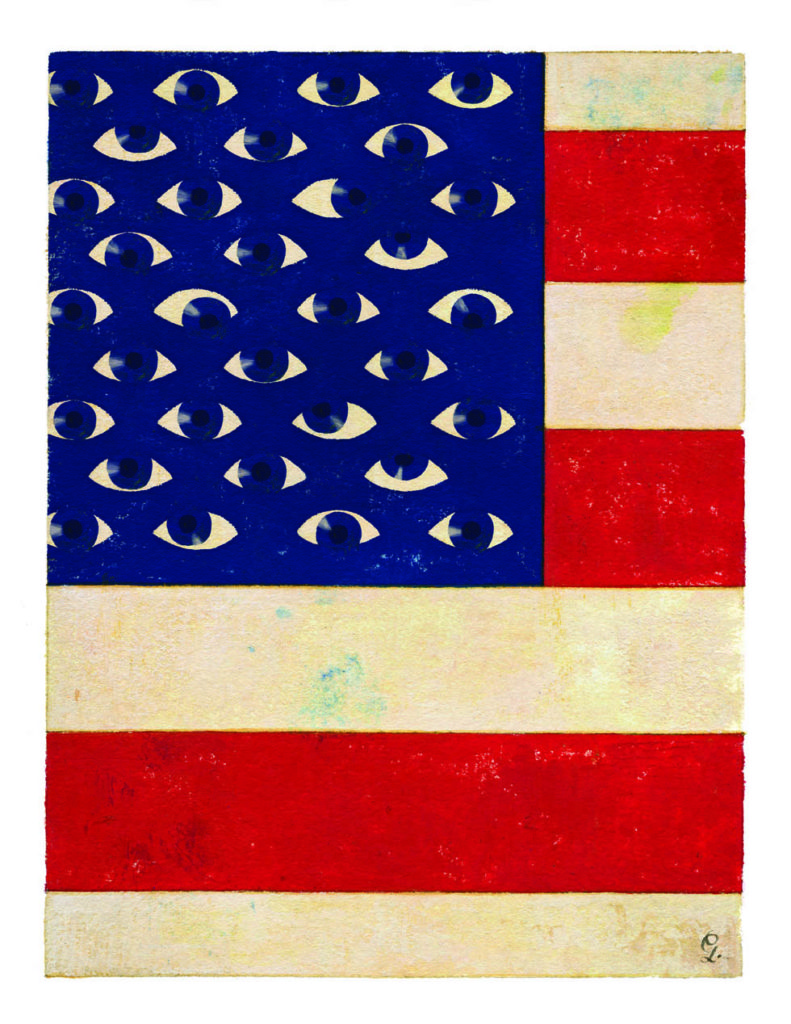
It may no longer be an exaggeration to say that big brother is watching. When Edward Snowden leaked classified government documents last year, many were surprised to learn just how much access the National Security Agency (NSA) has to the personal email and phone records of ordinary citizens. Those revelations about the scope and extent of surveillance by American intelligence agencies have prompted a national debate about civil liberties in an age of new technology that enables the government to both collect and store vast amounts of personal information about its citizens. The discussion is also surfacing in local communities where technology allows law enforcement to indiscriminately gather information on law-abiding citizens—information that is collected, kept, and shared with little to no oversight, or awareness by the general public.
Today, new technologies are changing the relationship between the citizen and the state, with the government and law enforcement able to access our information and observe our private activities, raising important civil liberties questions. Stanford Law School faculty and alumni are centrally involved in some of the most important questions surrounding this issue—working in key areas where the law is still catching up with technology.
Looming large over the debate is the post-9/11 war on terrorism, which has led to legislation such as the USA Patriot Act, designed to make it easier for the government to collect data that would help combat terrorism. At the same time, the incredible evolution in technology over the past two decades has revolutionized both the tools available to the government for surveillance and those used by individuals to live their lives.
“We’re living in the 21st century, but when it comes to issues concerning information technology, the law is still rooted in the 20th century,” says Anthony Romero, JD ’90, executive director of the American Civil Liberties Union (ACLU).
In striking a balance between constitutional rights, crime fighting, and national security, the legal doctrines at issue include everything from post-9/11 legislation that has given law enforcement access to electronic records, to constitutional rules governing criminal procedure, to the regulation of surveillance technology equipment by local governments.
Technology at the Local Level
The U.S. is a country of highways and cars, where Americans spend a lot of time behind the wheel. And tracking how we use our cars offers a picture of much more than simply our mode of transportation.
Automatic License Plate Reader/Recognition technology, ALPR, developed in the United Kingdom in the late 1970s, has been in use since the early 1980s as a tool to aid law enforcement agencies in various ways, from tracking stolen cars to identifying criminals. Since its introduction, this technology has become more powerful, mobile, and affordable. Today, more than 70 percent of police departments in the U.S. use some form of ALPR, recording thousands of plate numbers daily with cameras mounted on patrol cars and at key traffic areas such as highway overpasses and street lamps.
While capturing the license plate information, ALPR can also capture photos of the cars—and often the occupants, as well as where they live, where they shop, and where they drive. Put together, this technology can tell a story of how we go about our daily lives.
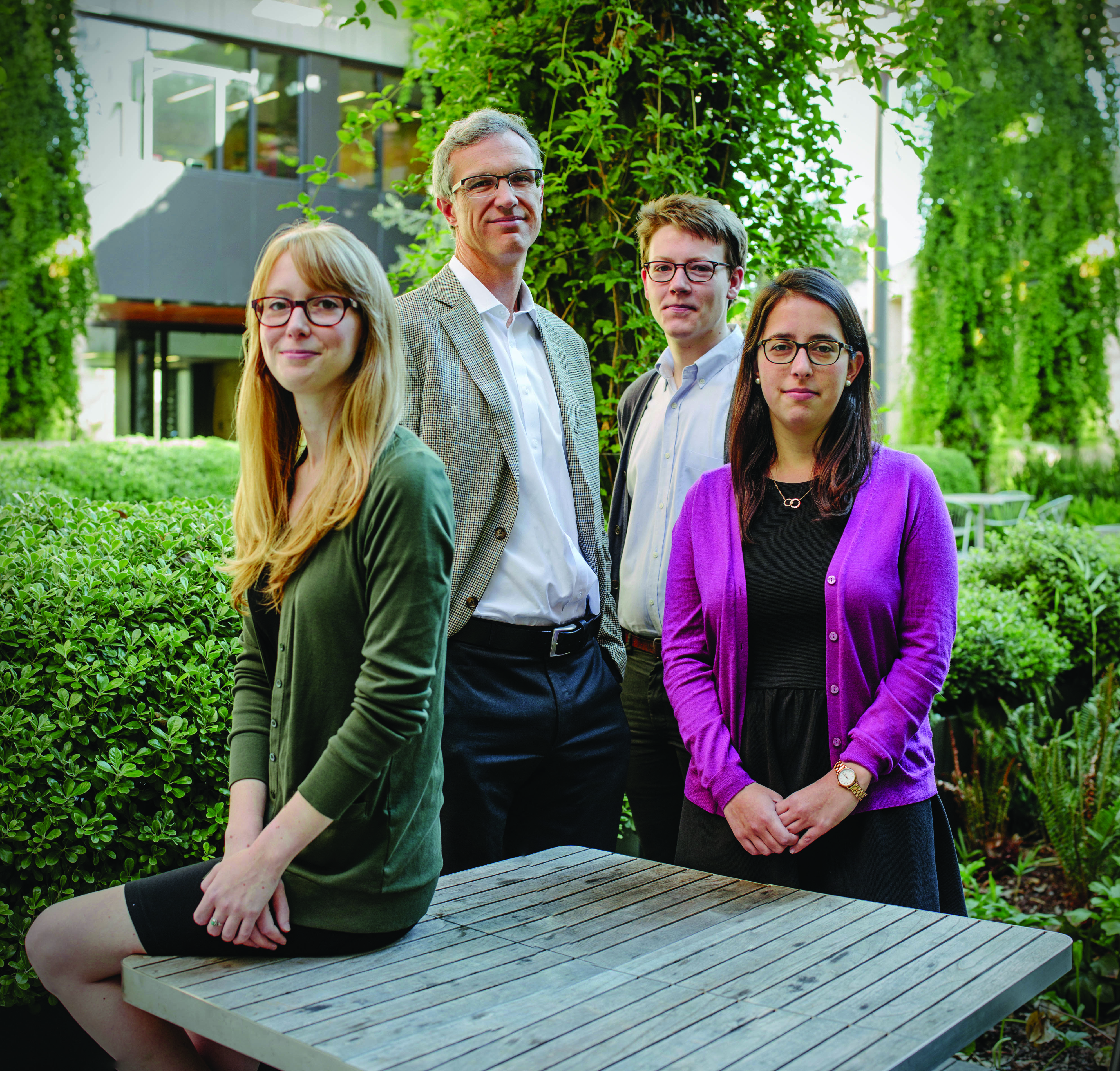
“Civil liberties problems arise when you engage in the mass tracking of hundreds of millions of Americans, most of whom are completely innocent of any wrongdoing,” says Catherine Crump, JD ’04 (BA ’00), who joined the Berkeley Law faculty this year as an assistant clinical professor of law and associate director of the Samuelson Clinic. She explains that technology is enabling the mass collection of data that can paint a detailed picture of how we interact, gleaning facts about us that the state couldn’t previously collect. As data storage has become more available and affordable, police departments are increasingly sharing gathered data regionally, and with the federal government, creating large databases of citizens, most of them law-abiding.
“No one denies that a license plate reader can be a useful investigative tool and it’s valuable to law enforcement to be able to check to see if a particular vehicle is stolen or associated with a suspected criminal,” says Crump, who was a staff attorney at the ACLU focusing on issues of government surveillance until earlier this year. “The civil liberties objection arises when law enforcement starts to pool massive amounts of location data and keep it for long periods of time based on the mere possibility that it might be useful someday. Because then you have a large database tracking people’s movements and that’s the type of information that can be misused.”
And currently, there are few regulations for how the data is used and how long it can be kept.
“There are no generally applicable laws placing limits, there are no federal laws,” she says. “In general it’s up to each state and law enforcement agency to come up with its own rules.”
Crump cites a few states that have introduced legislation for ALPR, including Utah, Maine, and New Hampshire, noting that it is largely a nonpartisan issue.
“It’s an issue where people on the left and right can find common ground between civil libertarian and law enforcement interests because everyone agrees that there are legitimate uses of the technology,” she says. “So the objections are not to the technology, but to certain uses.”
Crump thinks it important for all Americans to carefully consider these issues now, as new technologies are increasingly used by local law enforcement and the federal government.
“We should project forward to a world where it is possible to install a license plate reader on every street lamp,” she says. “And we should start planning for a world where that type of omnipresent surveillance is possible and figure out how we feel about it. And if people agree with my general view that that type of surveillance can be oppressive, it’s time to put rules and regulations in place to ensure that we take advantage of the positive aspects of this technology without suffering an undue loss to our civil liberties.”
Catherine Crump, JD ’04 (BA ’00)
New surveillance capabilities also raise concerns about how powerful investigatory tools typically reserved for investigations of criminal organizations may now be turned against certain communities.

“The government has a particular security interest in Muslim communities in the United States and abroad, yet these communities rarely have the political clout to resist overbroad surveillance,” says Shirin Sinnar, JD ’03, an assistant professor of law at Stanford.
Sinnar has written about the devastating mistakes made in associating people with terrorist activity in the United States––errors that have resulted from prejudicial attitudes, insufficient oversight, and lopsided incentives to err on the side of security. She has also noted cases in which the pervasive mapping, surveillance, and investigation of Muslim communities have “significantly harmed their ability to practice their faith and express their views.”
Crump offers an example of police surveillance of mosques. She explains that in 2012 as part of a program to gather information on the city’s Muslim community, the New York City Police Department mounted cameras directly outside of city mosques and used license plate-reading technology to record the identities of attendees and the cars they arrived in.
Although some of these practices have since been challenged in court, few have been resolved, Sinnar says. Most are dismissed for lack of standing or because the government invokes a national security-specific “state secrets” privilege, impeding any resolution of the constitutional questions at stake.
Reining in Mass Collection of Personal Data
In 2011, an unnamed telecommunications company received a demand from the Federal Bureau of Investigation (FBI) to hand over records about a customer (or customers). The demand came in the form of a National Security Letter (NSL), a type of legal demand that doesn’t require a court order and allows federal law enforcement to obtain information from telecommunications and Internet companies about their customers. NSLs have been issued by the government since about 1978, but the USA Patriot Act, passed overwhelmingly by Congress in 2001, greatly expanded their use. Critics have argued that the procedure raises major problems because NSLs lack judicial oversight and are almost always accompanied by a nondisclosure provision that prevents the recipient from revealing that it has received such a letter.
The company, whose name could not be revealed because of that secrecy order, challenged the NSL in court, arguing that both the nondisclosure provision and the limited judicial oversight were unconstitutional.
In March 2013, Judge Susan Illston, JD ’73, a federal district court judge in San Francisco, ruled that the statute authorizing the NSL violates the Constitution. In her decision, In re: National Security Letter, she wrote that even when “no national security concerns exist, thousands of recipients of NSLs are nonetheless prohibited from speaking out about the mere fact of their receipt of the NSL, rendering the statute impermissibly overbroad and not narrowly tailored.” She acknowledged “significant constitutional and national security issues at stake” and stayed her order to allow an appellate court to weigh in. The case was argued before the Ninth Circuit in October.
The case is one of a number of ongoing challenges to legislation that has expanded the government’s ability to access private data since the 9/11 attacks. Separately, the ACLU filed a lawsuit (now before the Second Circuit Court of Appeals) that challenges the government’s program of collecting phone records of all Americans under the Patriot Act. “It’s the first suit that hasn’t been kicked out because, thanks to Snowden, we can now establish standing—that is, show that the American public has been the subject of surveillance,” says Romero, who has met with Snowden twice in Moscow and is assisting with his legal counsel through the ACLU.
Meanwhile, some members of Congress are pushing to revise the Patriot Act in light of recent developments. Under pressure from the public as well as many Internet and telecommunications companies, Congress is considering limiting surveillance with the USA Freedom Act. While the House and Senate passed differing versions of the bill, both versions propose to rein in the collection of data by the NSA and other government agencies. The aim is to increase transparency of the Foreign Intelligence Surveillance Court (FISC), a federal court established under the Foreign Intelligence Surveillance Act (FISA) of 1978 to oversee requests for surveillance warrants against suspected foreign agents inside the United States. The FISC’s powers were extended under the Patriot Act to include domestic information collection when relevant to a counterterrorism investigation. The act also calls for narrowing of the requirement that businesses hand over customer data to the government and the creation of an independent constitutional advocate to argue cases before the FISC. So far, the bill is pending.
“The Senate version of the bill goes much farther than the tepid House version in strengthening the system of checks and balances and ensuring greater government transparency, but we still need to look more stringently at the operations of the judicial system and the oversight mechanisms of Congress,” says Romero.
With deadlines approaching, Congress is likely to act. “In June 2015, section 215, the law under which the phone records collection is happening, is set to expire. Congress will have to address the concerns raised by the telephony metadata program before then,” says Laura Donohue, JD ’07, professor of law at Georgetown Law, director of Georgetown’s Center on National Security and the Law, and co-director of the Center on Privacy and Technology.

National Security and Personal Privacy
In designing national security laws, the challenge for policymakers is to strike the right balance, says Jennifer Granick, civil liberties director at the Stanford Center for Internet and Society. “The big-picture issue is how do we protect national security and conduct foreign intelligence without creating a surveillance state,” she says.
Referencing the NSA’s program to obtain email and other private communications from Internet companies, she explains that “the government is engaged in a huge ‘dragnet’ in which an immense amount of information is getting sucked in about Americans as well as foreign targets. That raises all kinds of statutory and privacy questions. Is the law appropriate? Is the government collecting and using data lawfully and appropriately? Do we protect the rights of foreigners? When they get information about Americans, what do they do with it?”
“The three branches of the government were asleep at the switch when it came to protecting fundamental freedoms and privacy in the post 9/11 era,” says Romero. “The courts rubber-stamped the overzealous collection of data by the executive branch, and Congress exercised only limited oversight.”
Romero maintains that such acts have challenged not only the Fourth Amendment, which prohibits unreasonable search and seizures, but also the First Amendment, which prohibits the abridging of free speech and of the practice of religion.
“People who realize they’re being surveilled are less likely to write emails, place phone calls, and express themselves freely if they know they might be caught in government surveillance,” he says. “This will fundamentally change the way we live in our democracy.”
Granick asserts that a key priority should be ending government spying based on secret interpretations of law. “We don’t really know what laws the executive branch is following or how the Fourth Amendment and statutes already on the books are being interpreted. There’s an immense amount of classified information, including court opinions,” she says, referring to secret decisions of the FISC.
The Fight for Internet Freedom — featuring David Drummond, JD ’89 and Google VP
Ivan Fong, JD ’87, former general counsel of the Department of Homeland Security (DHS) agrees that data collection has to stay within constitutional limits, while lauding the importance of intelligence in national security investigations. “A certain amount of intelligence collection is, of course, necessary for the president to fulfill his constitutional duties and to act as commander in chief,” he says. “In a number of cases in which I was involved, the intelligence indeed played a significant role in preventing or disrupting actual terrorist threats.”
Fong is also sympathetic to civil liberties concerns. From 2009 to 2012, Fong was responsible for all legal determinations and regulatory policy at DHS. He provided legal counsel to the secretary of homeland security on questions of counterterrorism and national security law and policy and of cybersecurity law and policy. Fong believes current intelligence surveillance can both be lawful and serve our national security interests.
“Such collection should be, consistent with the law, as narrow as possible—in other words, a process known as minimization—and we should search for and embrace any new technological and other means to ensure stronger protection of privacy, civil rights, and civil liberties interests.”
Still, he agrees that courts, legislators, and policymakers “need to carefully articulate the core principles at stake to ensure outdated legal constructs or paradigms are reassessed in view of the new technology.” Fong points to the recent Supreme Court decision requiring police generally to obtain a warrant to search the contents of cell phones seized during an arrest as a good example of a case that updates existing legal doctrine in light of the power of new digital tools.
Riley: Redefining the Limits of Legal Search
That decision [Riley v. California, which the Court decided along with a related case, U.S. v. Wurie] recognizes that privacy in a digital world may require new rules and “brings the Fourth Amendment into the 21st century,” says Jeffrey Fisher, professor of law at Stanford and co-director of the Supreme Court Litigation Clinic.
It was Fisher who argued Riley before the Supreme Court in April, supported by the research and brief writing of his clinic students. The clinic represented David Riley, a college student currently serving a prison term in part due to evidence found on his cell phone that linked him to gang activities and a drive-by shooting.
In general, the Fourth Amendment allows police to search items that are found on a person who has been arrested, which could include a cell phone. But until Riley and Wurie, it wasn’t clear whether that right extended to police reading and reviewing data stored on the phone—before first obtaining a warrant.
“We argued that smart phones are categorically different from any other kind of non-digital object that can be found on a person because of the vast quantities of sensitive personal information involved and we argued that they should therefore not be subjected to search without a warrant,” says Fisher. Because the Supreme Court agreed with that argument unanimously, handing down its decision in June, in the future police will be able to seize but not search cell phones until a warrant has been obtained. Riley himself may be entitled to a new trial that excludes the cell phone evidence, which was obtained without a warrant.
The implications of the case could go well beyond the context of law enforcement and cell phones, and Fisher argues it will have implications in the national security context. “The Riley decision essentially rejects the argument that the government is currently using to justify the NSA’s collection of data on individuals, which is that digital data is subject to the same legal rules as analog data,” says Fisher.
The case also resolved a tough question about how to apply long-standing legal standards to new technologies. “This is a game changer, showing that the Court agrees that information gleaned from digital devices can paint a portrait of us that creates privacy considerations that didn’t exist before,” says Fisher.
Professor Jeffrey L. Fisherdiscusses the work he did with Stanford Supreme Court Litigation Clinic students preparing for the important digital privacy case.
Revisiting Third-Party Privacy Protection
One of the most serious places where the law has gone awry relates to the third-party doctrine, says Jonathan Mayer, JD ’13, a doctoral student in the computer science department who has taught Computer Security and Privacy at Stanford Law School.

According to Robert Weisberg, JD ’79, the Edwin E. Huddleson, Jr. Professor of Law, that legal theory, which evolved in the 1970s, holds that people do not have a reasonable expectation of privacy in information volunteered to third parties, such as banks, phone companies, and perhaps even email services. Without that expectation of privacy, the government may constitutionally obtain information from third parties without a warrant.
“It’s an anachronistic doctrine, because these days we give all sorts of private information to third parties, including cloud services. That’s the modern way of life, and the law needs to catch up,” says Mayer, whose online Stanford University course Surveillance Law this fall explores how U.S. law facilitates electronic surveillance—but also substantially constrains it.
“Given the changes in technology over the past few decades, we definitely need new laws that revisit the third-party doctrine of Fourth Amendment concerns,” affirms Weisberg.
This past spring, Weisberg guided students in a policy practicum to prepare a background study of legal and policy issues regarding state law enforcement access to user records held by communications companies. The study, done for the California Law Revision Commission, considered civil liberties, public safety, and the scope of federal preemption.
“Our recommendation was that statutes imposing a warrant requirement be established for law enforcement access to user records of cell phone providers, Internet service providers, social media companies, and other mobile and Internet-based communication providers and that they be very specific about what they do and do not allow,” says Weisberg, who is co-director of the Stanford Criminal Justice Center.
Such a revision in California statutory law, Weisberg explains, would address some problems, at least at the state level, with the Electronic Communications Privacy Act (ECPA), a federal regulation regarding the government’s ability to intercept electronic communications and to demand disclosure of stored communications, customer records, and other user data. ECPA has been criticized for failing to sensibly protect communications and consumer records, mainly because the law is so outdated and out of touch with how people share, store, and use information today.
Drones Coming Home
Use of unmanned aerial vehicles, or drones, by the military has increased dramatically as part of the effort to combat terrorism overseas. But use of drones in the U.S., for a variety of purposes, may also be on the rise.
High-altitude drones can hover over cities for long periods of time and record everything that takes place. But they are not widely adopted yet because the FAA has largely prohibited their use due to safety concerns with airplane traffic. But after passage of a provision in the FAA Modernization and Reform Act of 2012, drone use in the United States looks likely to increase. The act calls on the FAA to integrate unmanned aircraft by 2015 and to start by relaxing restrictions. Drones are already used to patrol the Mexican border and increasingly by businesses including agriculture. And local law enforcement agencies are now also exploring how they might be applied to crime fighting. Here again, new technology useful to law enforcement is raising questions about surveillance and mass collection of data, with regulations to safeguard the civil liberties of citizens not yet in place.
“Drones’ ability to track people and their movements raises huge privacy concerns,” says Romero. “There’s a serious lack of oversight on how they are being deployed and used, where data is being accessed and stored, and who has access to it.”
And the public seems to agree. Crump offers examples of two cities that have purchased drones but have then backtracked:
Seattle and San Jose. “When the purchase of drones became public, there was an uproar, with residents raising privacy concerns,” she says. In each case the program was shut down. “I think the idea of unmanned airborne vehicles hovering over people’s backyards and peering into their windows makes people deeply uncomfortable. Drones challenge people’s notions of privacy in a way that few other technologies have.”
A key concern with the introduction of this new surveillance technology is the lack of public review and consultation. “I think this raises important questions about the democratic process,” says Crump. “It’s what is known as ‘policymaking by procurement.’ Police departments simply acquire this equipment, often with funding from the federal government. And then they use it and it takes months or years for local government and the public at large to even learn about it.”
One exception—now—is Seattle. The city council passed an ordinance last year requiring the police department to first notify the council about surveillance purchases and to come forward with a proposal about how the information collected will be used.
Correcting the balance among social controls, governmental responsibilities for security, and individual liberty will require the public, Congress, and the courts understanding and navigating a maze of practices and policies, says Granick. “Over-classification, secret law, and intelligence jargon are getting in our way,” she says.
In reflecting on the secrecy regarding surveillance law and lack of robust oversight, Donohue observes, “The founders of the Constitution understood very deeply that not only must the government control the governed—but we must ensure that the government controls itself. Concentration of power in the hands of the few is the very definition of tyranny that the founders held—and that’s what we want to protect against, as we face issues of how government surveillance is being conducted in theglobal digital age.” SL

Maureen Coffey
“Can the law keep up with technology?” Yes and no. It was actually never the law (in my opinion) that could not keep up with technology, it was always a problem of detection and hence enforcement. This battle between crime investigation and enforcement never lacked legal framework. Poisoning (except by kings …) was always a crime, yet not all poisons were detectable. The invasion of privacy is a crime, but the means to do it are fast moving beyond enforceable detection. The more technology advances and no tangible damage can be seen (no broken windows, no finger prints, no “losses” – i.e. all passwords are “still there”) the less can law enforcement do about it. Once nano technology and quantum computing are advanced enough, we may not even know of any “intrusions” nor will the perpetrators themselves know (!) that in turn THEIR perimeters have been breached. Which may lead to interesting avoidance techniques by individualistic individuals that remind one of Amish lifestyles …